Fake Olympics shop ads on Meta target fans' wallets
Wed, 18th Feb 2026
Bitdefender Labs has identified a malvertising campaign on Meta platforms that uses fake "Olympics Shop" ads tied to the Milano Cortina 2026 Winter Olympic Games and directs users to cloned merchandise websites.
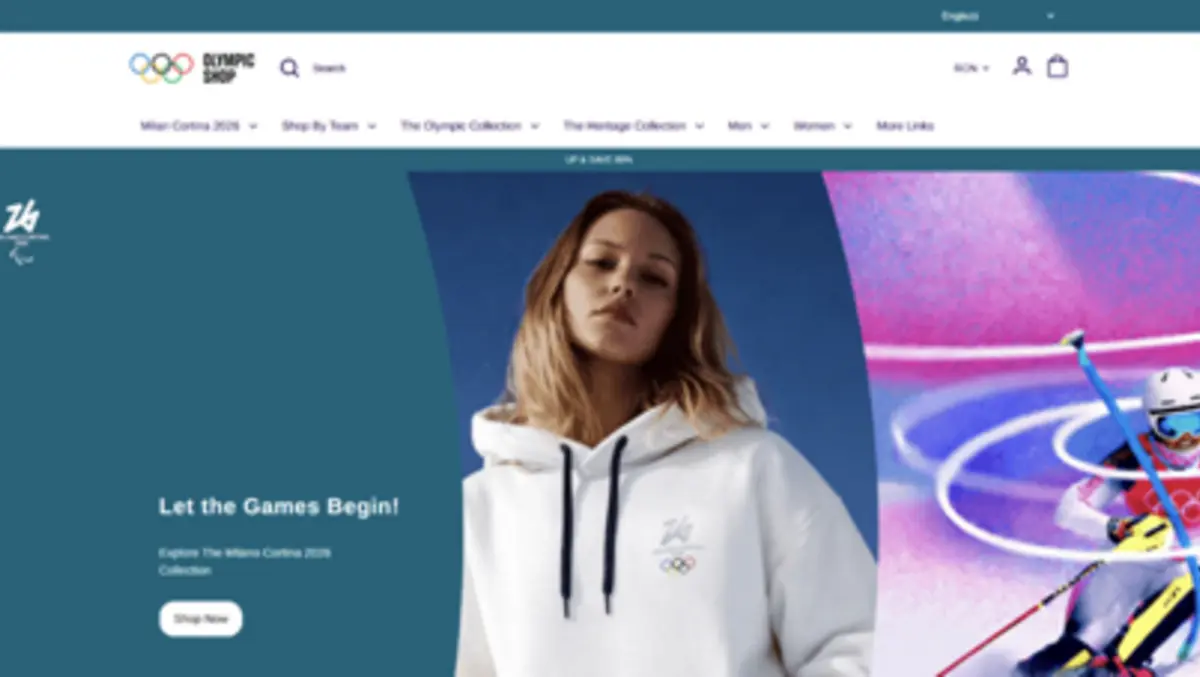
The ads claim discounts of up to 80% on "official" Olympics merchandise and use Olympic imagery, polished product photography and familiar promotional language. Examples cited by the researchers include "Olympics Exclusive! Up to 80% OFF" and "30 Days Free Return".
Clicking through takes users to near-identical copies of the official Olympics merchandise store. These clone sites mimic product collections, branding elements, colour schemes and layout, making them difficult to spot at a glance.
The campaign is designed to capture payments and personal data. Bitdefender says the fraudulent sites aim to steal credit card details at checkout and harvest information such as names, addresses, phone numbers and email accounts. It also flagged the risk of credential theft if users reuse passwords or attempt to log in via forms on the fake sites.
Victims also face consumer fraud: some buyers may receive counterfeit products, while others may receive nothing at all.
How the scam works
The operation hinges on small details many shoppers miss when moving quickly from a social media ad to checkout. Bitdefender highlighted subtle wording changes between legitimate promotions and scam variants. One example contrasts a genuine "Sign up & Save 15%" message with a scam version advertising "Sign & Save 80%".
Domain names and extensions are also used as bait. Many domains were registered within days of each other and used unfamiliar extensions such as ".top" or alternative ".shop" variations. In some cases, the ad preview appeared to show the official store before redirecting users to a different domain.
Researchers described the activity as coordinated. They observed clusters of lookalike domains registered daily, alongside newly created Facebook pages that launched discount campaigns soon after being set up. The pattern is rapid deployment: register a domain, clone a website, create a page, run ads, collect payments and then disappear.
These tactics are common around high-profile events, where fan excitement and time-limited offers can reduce scrutiny. Visual cloning further boosts success, as shoppers often rely on familiar branding and product imagery rather than checking the website address.
Broader sporting trend
Major sporting events have long attracted copycat fraud, from fake ticketing pages to unofficial merchandise offers. Bitdefender says this campaign fits a broader pattern of criminals exploiting global events with strong brand recognition and high purchase intent.
It warned similar campaigns could surface in Australia as other major sporting moments approach, including the Winter Olympics, the Australian Grand Prix and the FIFA World Cup. Social media ads remain a key channel because they can be launched quickly and targeted at audiences showing interest in specific events and merchandise.
While this research focused on Meta platforms, the tactic is not tied to any single ad system. Fraudulent ads can migrate across networks and reappear under new page names and domains when older ones are removed.
What to watch for
Bitdefender's guidance focuses on basic checks to reduce the risk of cloned storefronts. It advises scrutinising the domain and treating newly registered domains and unfamiliar extensions as warning signs. Shoppers should look beyond visuals and check the URL for small differences in spelling or structure.
Extreme discounts are another red flag. An 80% reduction on official merchandise should prompt extra verification before entering payment details. Bitdefender also pointed to Facebook Page transparency information, which can show whether a page was created recently and whether it has a genuine history and engagement.
The company recommended using link-checking and scam-analysis tools before clicking, including its Link Checker and an AI-enabled tool called Bitdefender Scamio. It also advised consumers not to rush purchases and to use layered security protections that can detect scam domains.
"When scam sites mirror official branding almost perfectly, users default to visual familiarity instead of domain verification, a common behaviour that attackers count on for the success of their scams," Bitdefender Labs said.