HID stories - Page 46
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

Surge in encrypted malware prompts warning about detection strategies

APAC parents hide internet activity from children more than cyber attackers

Keyfactor and Primekey announce partnership to automate PKI

UPDATED: F5 being sued by company that claims to own NGINX

In IT security, 'good enough' is no longer good enough

Ransomware attacks swell, average ransom payments rise - report

Hands-on preview: The Last of Us Part II

DNS recursive resolvers vulnerability can launch DDoS attacks against any victim

Five wine-tasting tips that should be applied to network security

Pega strives to rid AI-based CX systems of discrimination

Minecraft adds five new worlds to RTX beta on Windows 10

Digital heists: Attacks on financial institutions rise 238% in 3 months
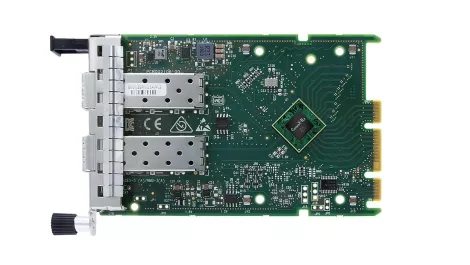
NVIDIA announces new Mellanox SmartNIC for the modern data center

HID Global and Keyfactor team up for zero-trust security

VPN provider Hide My Ass promises no more user logging

Hands-on Review: The ROG STRIX Go 2.4 headset has it all

CenturyLink launches solution to combat insider threats

Why AI and ML are increasingly important for effective IT security

Three ways to protect your business in the cloud
